It rarely arrives with a warning.
One day, your brand is operating normally. Then someone on your team notices something: a pattern of negative reviews appearing on Google and Trustpilot in quick succession. A critical article in a trade publication that reads less like journalism and more like a briefing document. A rumour circulating in your industry that seems too specific to be organic. A sudden drop in branded search traffic that your SEO team cannot explain.
Competitive reputation attacks are more common than most business leaders want to admit — and far more sophisticated than they used to be. In an environment where a single page of search results or an AI-generated summary can define how a prospect perceives your brand, the ability to damage a competitor’s reputation without leaving fingerprints has never been easier.
This guide is for the leaders who find themselves on the receiving end. Here is how to respond — methodically, strategically, and effectively.
Step 1: Confirm What You Are Dealing With
Before you do anything, resist the instinct to react. The first and most important step is to establish whether you are actually under a coordinated attack or whether you are dealing with organic negative sentiment that happens to have spiked.
The distinction matters enormously. Responding to a coordinated attack as if it were organic feedback — by, for example, publicly engaging with fake reviews or issuing defensive statements — can amplify the problem and signal to the attacker that their campaign is working.
Look for these indicators of a coordinated campaign:
Unusual velocity. A sudden cluster of negative reviews, articles, or social media posts appearing within a short window is rarely coincidental. Organic negative sentiment tends to accumulate gradually. Coordinated attacks tend to spike.
Unusual specificity. Generic negative reviews (“bad company, do not use”) are typically organic. Reviews or articles that reference specific internal details, use consistent language across multiple sources, or make claims that would require inside knowledge suggest coordination.
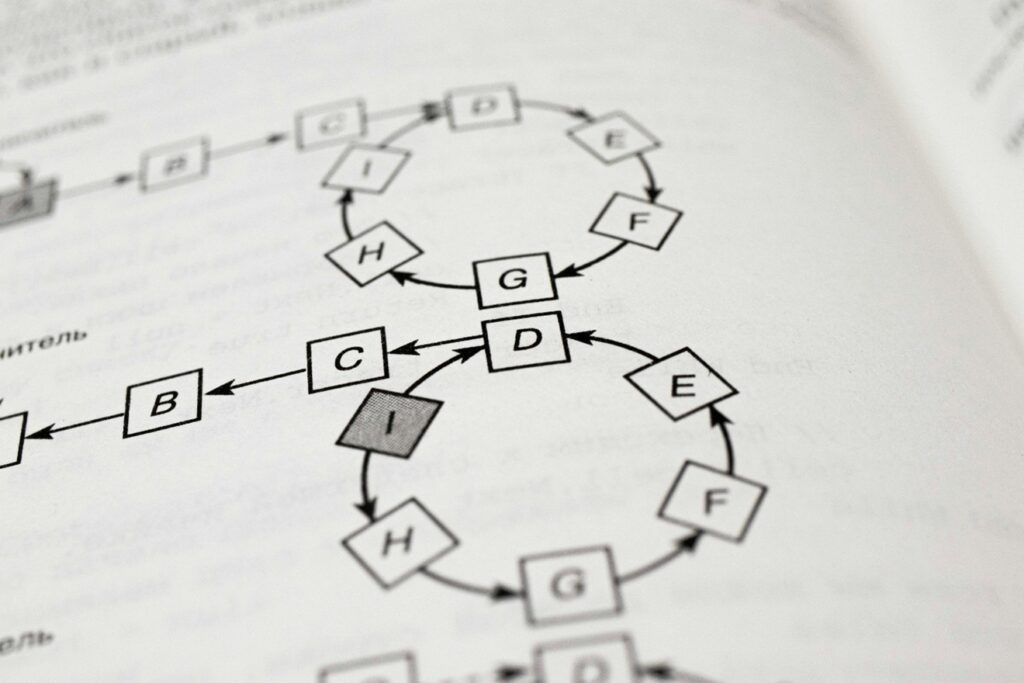
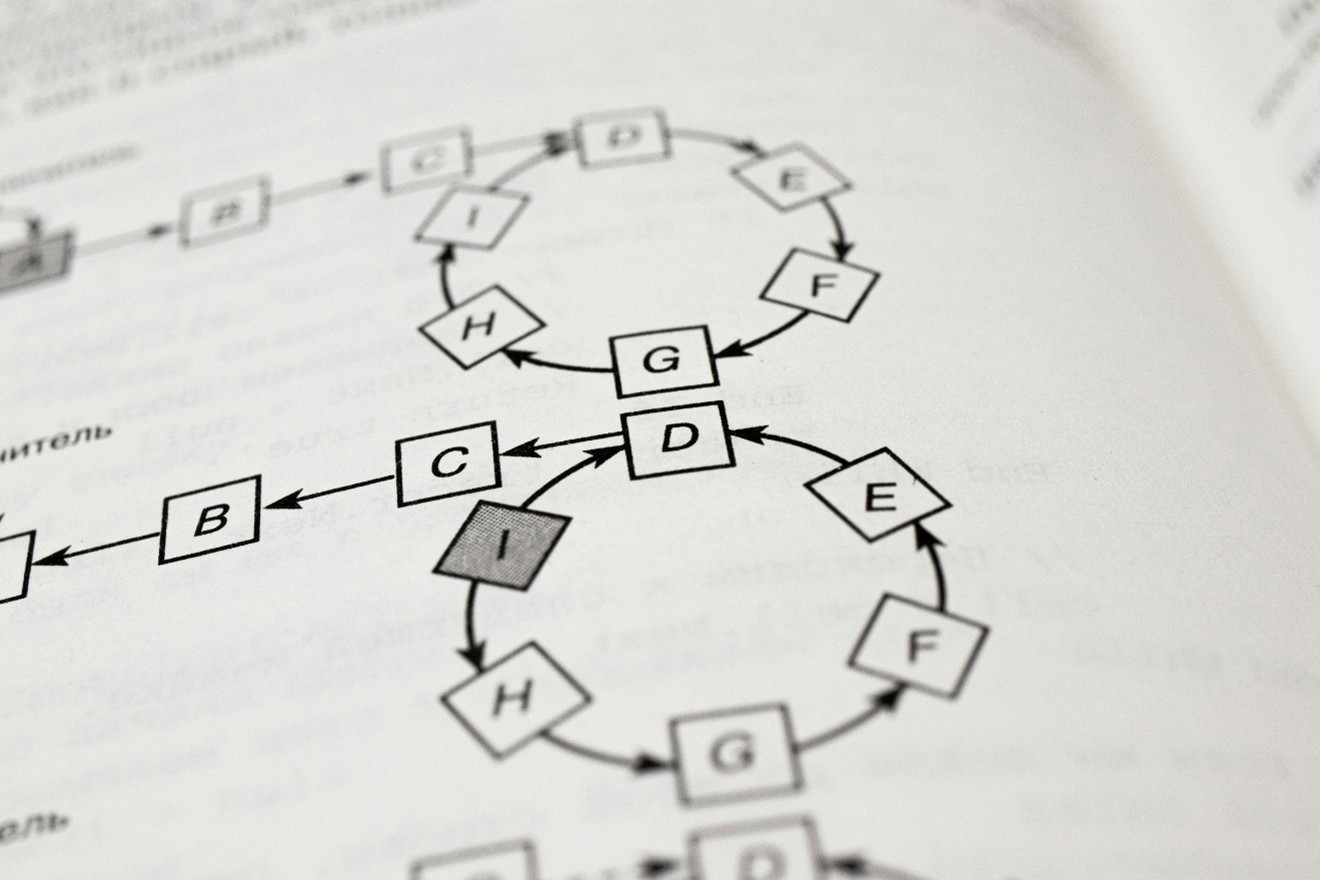
Traceable patterns. New accounts with no history. Reviews from profiles that have only ever reviewed your company. Articles that cite each other circularly. Social media posts that use identical or near-identical phrasing. These are fingerprints.
Timing. Attacks frequently coincide with commercially sensitive moments — a product launch, a funding announcement, a key tender process, a period of leadership transition. If the timing feels deliberate, it probably is.
Step 2: Document Everything Before You Touch Anything
This is the step most companies skip in their urgency to respond, and it is the one they most often regret.
Before removing, responding to, or engaging with any negative content, document it comprehensively. Screenshot every review, article, and social post with timestamps and URLs. Archive web pages using tools like the Wayback Machine. Record the metadata where available. If the attack escalates into legal territory — and coordinated reputation attacks sometimes do — this documentation becomes the foundation of any action you take.
Do not ask your team to respond to negative reviews yet. Do not issue a public statement. Do not contact the publication that ran the critical article. Not yet.
Step 3: Audit Your Current Exposure
While documentation is underway, conduct an honest audit of your current digital vulnerabilities. Ask yourself: if a prospect searched your brand name right now, what would they find? What does ChatGPT say about your company? What does Gemini surface? What appears in the knowledge panels and AI overviews that increasingly sit above organic search results?
Understanding your baseline exposure tells you two things: how much damage has already been done, and where your defensive gaps are. Companies with strong, authoritative digital presences — robust owned content, consistent knowledge graph entries, high-authority media placements — are significantly harder to attack and faster to recover. Companies with thin or neglected digital footprints are disproportionately vulnerable because negative content faces less competition for visibility.
Step 4: Build Your Counter-Architecture
Reputation defense in the modern media environment is not primarily about removal — though removal has its place. It is about displacement and dilution.
The goal is to surround the negative content with so much high-quality, authoritative, positive content that the attack loses its oxygen. In practice, this means:
Accelerate owned content production. Publish thought leadership articles, executive commentary, case studies, and company news at an increased cadence. Fresh, authoritative content signals relevance to search engines and provides AI platforms with accurate, positive material to draw from.
Activate your earned media relationships. Now is the time to call in favours with journalists and editors you have relationships with. A well-placed profile piece or industry commentary in a respected publication carries significant weight in displacing negative search results.
Strengthen your knowledge infrastructure. Ensure your brand is accurately and substantively represented in the databases and platforms that feed AI models — Google’s Knowledge Graph, Wikidata, and industry directories. These assets are often overlooked but carry considerable authority in shaping AI-generated summaries.
Pursue removal where it is viable. For fake reviews, most platforms have a reporting mechanism for content that violates their terms of service — use it systematically and document every submission. For defamatory content, seek legal advice before engaging. For outdated or inaccurate articles, a direct approach to the publication is sometimes effective, though it requires careful handling.
Step 5: Consider Whether to Go Public
This is the most delicate judgment call in the process, and there is no universal answer.
In most cases, publicly naming a competitor as the source of a reputation attack — even when you are confident of it — carries significant risk. It escalates the conflict, invites media scrutiny of both parties, and can make your brand appear defensive or embattled. The attacker, in many cases, is hoping for exactly this response.
The stronger play is usually to win quietly: rebuild your digital presence, displace the negative content, and let the attack fade for lack of traction. If the attack has crossed into clearly defamatory or illegal territory, pursue legal remedies through appropriate channels rather than public accusation.
The exception is if the attack is so visible and so clearly coordinated that silence itself becomes damaging — in which case a carefully worded, measured public statement that focuses on facts rather than accusations can be appropriate. The keyword is measured. Emotion is your enemy in this situation.
Step 6: Use the Attack to Build Long-Term Resilience
Every reputation attack, however uncomfortable, reveals something useful: where your defenses were thin.
The companies that emerge strongest from these situations are the ones that treat the attack as a forcing function — an event that accelerates the investment in digital presence and reputation infrastructure they should have made earlier. Build the personal website. Commission the thought leadership programme. Maintain the media relationships. Update the knowledge graph entries. Do the unglamorous work of making your brand hard to attack.
Because the next one will come when you are least expecting it. The question is whether you will be ready.